ASLR in Windows
Windows supports Address Sace Layout Randomization (ASLR). [WindowsInternal] [1] desribes the detail on how executable images, DLL, stack, heap are randomized.
Figure 3-1 Windows OS space layout, source: [WindowsInternal] [1]
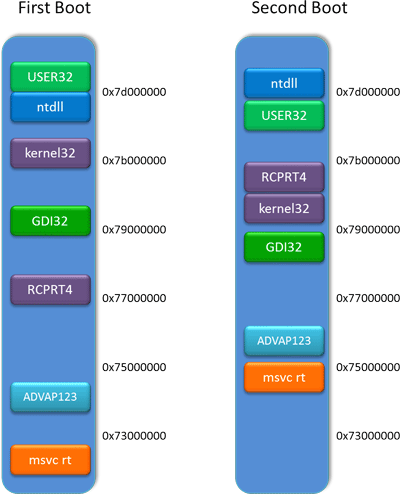
[ASLR1][2] shows the Windows8 HE-ASLR design and entropy number.
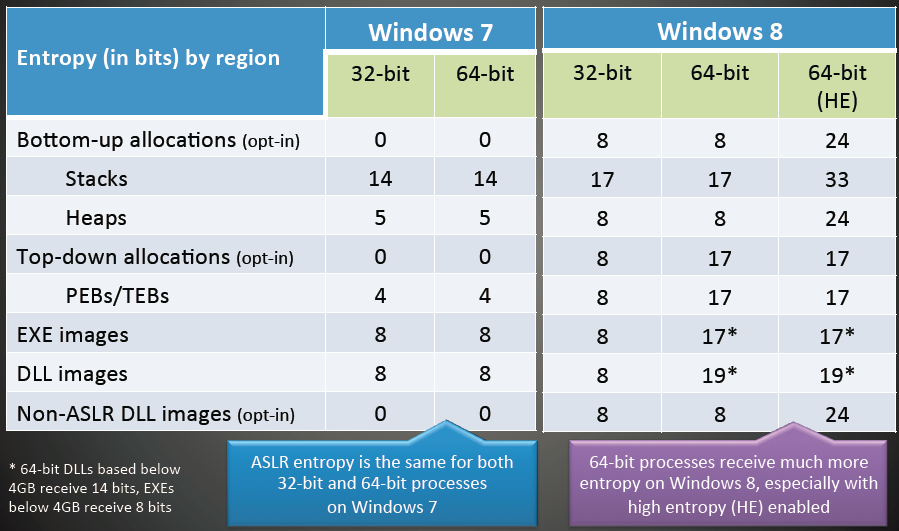
[ASLR2][3] shows different image layouts during boot.
The following Diagram showing how the physical memory location of various system DLLs changes between a first and second boot
[1] [WindowsInternal] Windows Internals, 6th edition, Mark E. Russinovich, David A. Solomon, Alex Ionescu, 2012, Microsoft Press. ISBN-13: 978-0735648739/978-0735665873
[2][ASLR1] Exploit Mitigation Improvements in Windows 8, Ken Johnson, Ma, Miller
Last updated